With the luxury of using Microsoft Intune, alongside configuration policies, you can get a device set up quickly and efficiently just by enrolling it. I prefer some applications to be a Baseline, so we know that every device within a company has program X, Y & Z and one of those is Defender for Endpoint (Microsoft’s paid version of Defender).
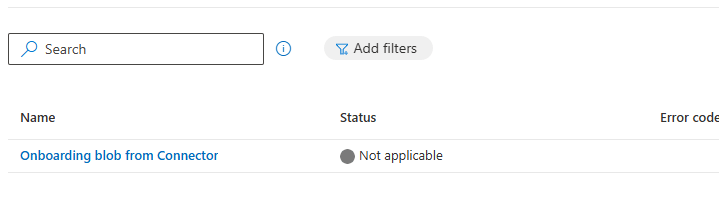
In this post I’m going to show what happens, when you receive the following;